A simple guide to how the S2SCORE helps organizations limit liability.
Disclaimer: SecurityStudio is not a law firm. For specific legal questions, please seek the advice of a licensed attorney.
Introduction
Although we aren’t lawyers, we’ve been involved in enough breaches, incidents, and legal proceedings to offer good advice about how a S2SCORE can help you limit liability after a breach, or avoid it altogether.
If you’d like to skip the background information and learn about the importance of the S2SCORE assessment in protecting you from legal liability, go to the FAQs.
You will have a breach
They say that there’s no guarantees in information security. This is not true. There are at least two of them.
The first guarantee is a breach. You are guaranteed to have a breach. Factually, no matter what you do, no matter how much money you spend, and no matter how blinky your blinky lights are, you cannot possibly prevent a breach with 100% certainty. A breach is guaranteed, given enough time.
The second guarantee is after a breach occurs, you must defend yourself. It’s human nature to look for someone to blame and to hold someone accountable in bad situations such as a data breach. You’ll need a defense in the boardroom, with customers, with regulators, in the court of public opinion, and/or the court of law. Our “accusers” are board members, customers, regulators, the public, and those who perceive that they’ve been done wrong (represented legal counsel).
We’ll collectively call this group the “accusers”. They have a right to accuse you/us because they’ve been negatively affected by the situation.
So, what about liability?
Liability is related to negligence. Where there is negligence, there’s liability.
A failure to behave with the level of care that someone of ordinary prudence would have exercised under the same circumstances. The behavior usually consists of actions but can also consist of omissions when there is some duty to act (e.g., a duty to help victims of one’s previous conduct). (Source: Cornell Law School – https://www.law.cornell.edu/wex/negligence)
A key question from our accusers will be “what did you do to prevent this (breach) from happening?” The common follow-up question is “did you do what a reasonable person would do in similar circumstances?” The first question determines your actions the second question determines if your actions were negligent.
Liability with/without S2SCORE
A reasonable person understands the importance of an information security risk assessment. The risk assessment shows that the organization has taken information security seriously enough to diagnose its problems. Diagnosis of problems is always the first step towards improving (or fixing) your problems. Spending money to fix something without a diagnosis can add to the hurt (liability) because you have less basis to defend how and why you’ve spent the information security budget that you have.
You must perform a diagnosis before fixing problems. Fixing problems without a diagnosis is illogical and irresponsible. Can you fix a car without a diagnosis? The answer is no. You also can’t fix information security without a diagnosis ( S2SCORE ).
The result of not conducting an information security risk assessment is ignorance. Ignorance rears its ugly head for several reasons, and most of the reasons are based on false logic. We’ve heard the false logic in statements such as:
- If I know about the problems, then I’ll have to fix them.
- I don’t want to know about information security because then I’d have to address it.
Ignorance is less defensible than it’s ever been given today’s current threats. Some will argue that ignorance isn’t defensible at all.
With a risk management assessment and a S2SCORE the organization can show that it took a reasonable step in preventing the breach by diagnosing problems in their own security program. This simple step limits liability.
Three additional features of the S2SCORE that reduce liability more:
- The assessment is objective, meaning the assessor doesn’t only rely on his/her own opinions. Defending opinions is much harder than defending objective yes/no, true/false questions.
- The assessment is scored. Scoring is important to show future improvements, and improvements improve defensibility.
- The S2SCORE is used by more than 1,000 other organizations. There’s always more defense in the herd.
To summarize, no risk assessment means more liability (probably). Performing an information security risk assessment, such as S2SCORE means less liability (probably).
FAQs
Q. Can a S2SCORE help me in a lawsuit?
A. Absolutely. The S2SCORE shows that the organization takes information security seriously and that it’s willing to tackle their problems (as opposed to ignoring them).
Q. When can a S2SCORE hurt me in a lawsuit?
A. The only time we’ve seen or hypothesized that a S2SCORE could hurt you is if you have a low/poor score, and you haven’t done anything about it. Here’s a real example.
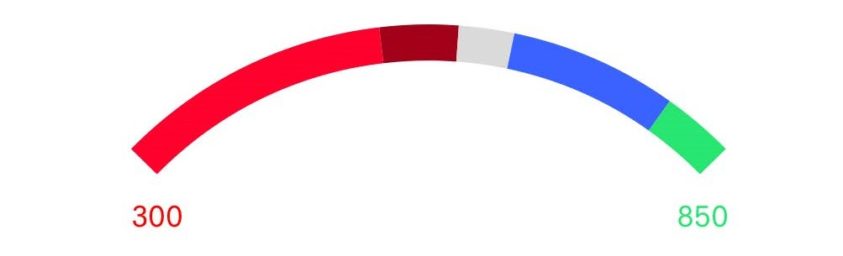
An organization does an assessment and received a S2SCORE of 479 (scale 300 – 850). The organization reviewed the results and created a simple roadmap to make security better (and improve their score). After three months, the S2SCORE raised to a 501. A 501 is still poor, but the improvement from a 479 makes this organization much more defensible. If the organization had just sat on their 479 S2SCORE without making any improvements, the S2SCORE could have potentially hurt them.
Q. If I don’t do an information security risk assessment, such as S2SCORE, am I more liable?
A. The likely answer is yes. In our opinion, and the opinion of most others, a risk assessment is a required first step in information security and it’s also a required step in confirming the effectiveness of the information security. Logically, these additional questions make sense:
- How can you possibly know where your risk is if you haven’t assessed it?
- How do you know if your information security investments are being spent wisely, where they will have the most positive effect?
The S2SCORE were built to provide capable, but easy-to-understand guidance to organizations for improving information security and proving due care.
Conclusion
There are many questions posed in this brief article. They were included on purpose. When you’re facing your accusers after a data breach (which is guaranteed), you will need to have your own answers. Consider each of these questions posed in this article and prepare your own answers ahead of time. Don’t wait until you lose control of the message. If you haven’t done an information security risk assessment, like the S2SCORE, know that you are probably less defensible and you’re more likely to be found liable. That’s just the truth.
About SecurityStudio
SecurityStudio is a collaborative company that provides common sense, best-in-class information security tools to the information security community. We invite partners, organizations, and people from all walks to participate in our mission of “fixing the broken industry.”